Educational institutes data are the one needs more security. Here are some preventions to protect your data from WannaCry Ransomware.
What is WannaCry ransomware?
There are various types of malware that affect your computer, from those that steal your information & those that just delete everything on the particular device. Ransomware, as the name, prevents users to access their devices and data till a certain ransom is paid to its creator. Ransomware locks computers encrypt the data on it and prohibit software and apps from running.
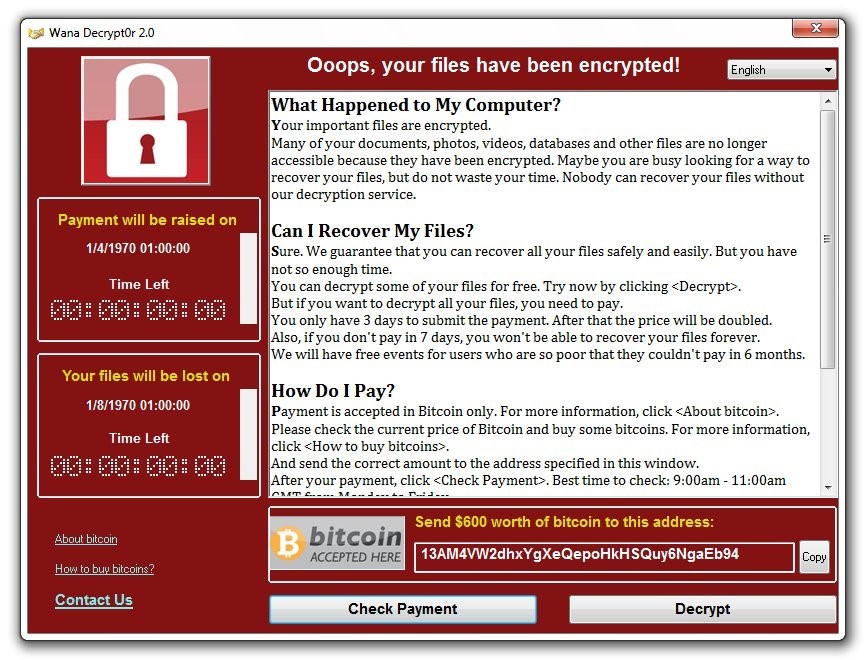
WannaCry is ransomware, a growing category of powerful accused malware. Once it is activated on a machine, it encrypts the files on that machine so they are inaccessible. Then it directs the owner to pay a ransom in Bitcoin in exchange for liberating the files.
Reference: Symantec
Who was behind the attack and What was their motivation?
It is not known yet. Though, it is generally accepted that the hackers used the ‘Eternal Blue Hacking Weapon’ establish by America’s National Security Agency (NSA) to access to Microsoft Windows computers used by terrorist outfits and enemy states.
Since over a thousand computers in the Russian Interior Ministry, as well as computers in China, were hit, some of the state or quasi-state actors suspected of carrying out large-scale break-ins of computer systems in the United States will, on this demand, start as not being Instant suspects. Interestingly, the NSA tool was stolen in April by a group called Shadow Broker, who seemed unhappy with US President Donald Trump, whom they said they had voted for.
Pradipto Chakrabarty, Regional Director, CompTIA India, said that the linking of Aadhaar to bank accounts, income tax, and other sensitive information increases the “threat”. “Since the user’s bank account is linked with his Aadhaar number, the ransomware can possibly lock down the account and make it unusable unless a ransom is paid,” Chakrabarty said.
Amit Nath, Head of Asia Pacific, Corporate Business, at F-Secure Corporation, said the realization of the WannaCry ransomware attack could give hostile nation states bounds to create cyber weapons where there’s no hope of recovering the data. “That’s the worst-case scenario,” Amit Nath said.
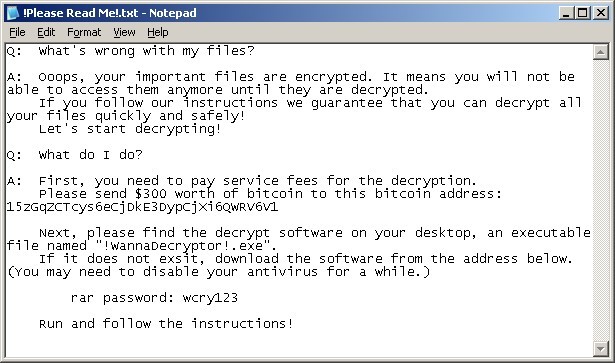
It also drops a file named!Please Read Me!.txt which have the text explaining what has happened and how to pay the ransom.
Reference: Symantec
Indicators of compromise:
Ransomware is writing itself into a random character folder in the ‘ProgramData’ folder with the file name of “tasksche.exe” or in ‘C:\Windows\’ folder with the filename “mssecsvc.exe” and “tasksche.exe”.
Ransomware is granting full access to all files by using the command:
Icacls . /grant Everyone: F /T /C /Q
Using a batch script for operations:
176641494574290.bat
Reference: Cyber Swachhta Kendra
Best practices to prevent ransomware attacks:
- Perform regular backups.
- Establish a Sender Policy Framework (SPF), Domain Message Authentication Reporting and Conformance (DMARC), and DomainKeys Identified Mail (DKIM) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Don’t open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an unsolicited e-mail, even if the link seems benign. In cases of genuine URLs close out the e-mail and go to the organization’s website directly through browser.
- Restrict execution of PowerShell /WSCRIPT in enterprise environment Ensure installation and use of the latest version (currently v5.0) of PowerShell, with enhanced logging enabled. script block logging and transcription enabled. Send the associated logs to a centralized log repository for monitoring and analysis.
- Application whitelisting/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA%, %PROGRAMDATA%, and %TEMP% paths. Ransomware sample drops and executes generally from these locations. Enforce application whitelisting on all endpoint workstations.
- Deploy web and email filters on the network. Configure these devices to scan for known bad domains, sources, and addresses; block these before receiving and downloading messages. Scan all emails, attachments, and downloads both on the host and at the mail gateway with a reputable antivirus solution.
- Disable macros in Microsoft Office products. Some Office products allow for the disabling of macros that originate from outside of an organization and can provide a hybrid approach when the organization depends on the legitimate use of macros. For Windows, specific settings can block macros originating from the Internet from running.
- Configure access controls including file, directory, and network share permissions with least privilege in mind. If a user only needs to read specific files, they should not have write access to those files, directories, or shares.
- Maintain updated Antivirus software on all systems.
- Consider installing Enhanced Mitigation Experience Toolkit, or similar host-level anti-exploitation tools.
Block the attachments of file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsf
Regularly check the contents of backup files of databases for any unauthorized encrypted contents of data records or external elements, (backdoors /malicious scripts.) - Keep the operating system third party applications (MS office, browsers, browser Plugins) up-to-date with the latest patches.
- Follow safe practices when browsing the web. Ensure the web browsers are secured enough with appropriate content controls.
- Network segmentation and segregation into security zones – help protect sensitive information and critical services. Separate administrative network from business processes with physical controls and Virtual Local Area Networks.
- Disable remote Desktop Connections, employ least-privileged accounts.
- Ensure integrity of the codes /scripts being used in database, authentication and sensitive systems, Check regularly for the integrity of the information stored in the databases.
- Restrict users’ abilities (permissions) to install and run unwanted software applications.
- Enable personal firewalls on workstations.
- Implement strict External Device (USB drive) usage policy.
- Employ data-at-rest and data-in-transit encryption.
- Carry out vulnerability Assessment and Penetration Testing (VAPT) and information security audit of critical networks/systems, especially database servers from CERT-IN empaneled auditors. Repeat audits at regular intervals.
- Individuals or organizations are not encouraged to pay the ransom, as this does not guarantee files will be released. Report such instances of fraud to CERT-In and Law Enforcement agencies.
Reference: Cyber swachhta Kendra
For more such updations stay connected & read our blogs…